Getting Started with Citrix ADC
Deploy a Citrix ADC VPX instance
Optimize Citrix ADC VPX performance on VMware ESX, Linux KVM, and Citrix Hypervisors
Apply Citrix ADC VPX configurations at the first boot of the Citrix ADC appliance in cloud
Install a Citrix ADC VPX instance on Microsoft Hyper-V servers
Install a Citrix ADC VPX instance on Linux-KVM platform
Prerequisites for Installing Citrix ADC VPX Virtual Appliances on Linux-KVM Platform
Provisioning the Citrix ADC Virtual Appliance by using OpenStack
Provisioning the Citrix ADC Virtual Appliance by using the Virtual Machine Manager
进行guring Citrix ADC Virtual Appliances to Use SR-IOV Network Interface
进行guring Citrix ADC Virtual Appliances to use PCI Passthrough Network Interface
Provisioning the Citrix ADC Virtual Appliance by using the virsh Program
Provisioning the Citrix ADC Virtual Appliance with SR-IOV, on OpenStack
进行guring a Citrix ADC VPX Instance on KVM to Use OVS DPDK-Based Host Interfaces
Deploy a Citrix ADC VPX instance on AWS
Deploy a VPX high-availability pair with elastic IP addresses across different AWS zones
Deploy a VPX high-availability pair with private IP addresses across different AWS zones
进行gure a Citrix ADC VPX instance to use SR-IOV network interface
进行gure a Citrix ADC VPX instance to use Enhanced Networking with AWS ENA
Deploy a Citrix ADC VPX instance on Microsoft Azure
Network architecture for Citrix ADC VPX instances on Microsoft Azure
进行gure multiple IP addresses for a Citrix ADC VPX standalone instance
进行gure a high-availability setup with multiple IP addresses and NICs
进行gure a high-availability setup with multiple IP addresses and NICs by using PowerShell commands
进行gure a Citrix ADC VPX instance to use Azure accelerated networking
进行gure HA-INC nodes by using the Citrix high availability template with Azure ILB
进行gure HA-INC nodes by using the Citrix high availability template for internet-facing applications
进行gure a high-availability setup with Azure external and internal load balancers simultaneously
Upgrade and downgrade a Citrix ADC appliance
Authentication, authorization, and auditing application traffic
-
-
-
-
-
-
Persistence and persistent connections
Advanced load balancing settings
Gradually stepping up the load on a new service with virtual server–level slow start
Protect applications on protected servers against traffic surges
Retrieve location details from user IP address using geolocation database
Use source IP address of the client when connecting to the server
Use client source IP address for backend communication in a v4-v6 load balancing configuration
Set a limit on number of requests per connection to the server
进行gure automatic state transition based on percentage health of bound services
Use case 2: Configure rule based persistence based on a name-value pair in a TCP byte stream
Use case 3: Configure load balancing in direct server return mode
Use case 6: Configure load balancing in DSR mode for IPv6 networks by using the TOS field
Use case 7: Configure load balancing in DSR mode by using IP Over IP
Use case 10: Load balancing of intrusion detection system servers
Use case 11: Isolating network traffic using listen policies
Use case 12: Configure Citrix Virtual Desktops for load balancing
Use case 14: ShareFile wizard for load balancing Citrix ShareFile
Use case 15: Configure layer 4 load balancing on the Citrix ADC appliance
-
-
-
Authentication and authorization for System Users
-
进行guring a CloudBridge Connector Tunnel between two Datacenters
进行guring CloudBridge Connector between Datacenter and AWS Cloud
进行guring a CloudBridge Connector Tunnel Between a Datacenter and Azure Cloud
进行guring CloudBridge Connector Tunnel between Datacenter and SoftLayer Enterprise Cloud
进行guring a CloudBridge Connector Tunnel Between a Citrix ADC Appliance and Cisco IOS Device
CloudBridge Connector Tunnel Diagnostics and Troubleshooting
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde.(Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique.(Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica.(Aviso legal)
此内容已经过机器动态翻译。放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다.책임 부인
Este texto foi traduzido automaticamente.(Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt.(Haftungsausschluss)
Ce article a été traduit automatiquement.(Clause de non responsabilité)
Este artículo ha sido traducido automáticamente.(Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
VIP scaling support for Citrix ADC VPX instance on GCP
A Citrix ADC appliance resides between the clients and the servers, so that client requests and server responses pass through it. In a typical installation, virtual servers configured on the appliance provide connection points that clients use to access the applications behind the appliance. The number of public virtual IP (VIP) addresses needed for a deployment varies on a case-by-case basis.
The GCP architecture restricts each interface on the instance to be connected to a different VPC. A VPC on GCP is a collection of subnets, and each subnet can span across zones of a region. In addition, GCP imposes the following limitation:
- There is a 1:1 mapping of number of public IP addresses to number of NICs. Only one public IP address can be assigned to a NIC.
- A maximum of only 8 NICs can be attached on a higher capacity instance type.
For example, an n1-standard-2 instance can have only 2 NICs, and the Public VIPs that can be added is limited to 2. For more information, seeVPC resource quotas.
To achieve higher scales of public virtual IP addresses on a Citrix ADC VPX instance, you can configure the VIP addresses as part of the metadata of the instance. The ADC VPX instance internally uses forwarding rules provided by the GCP to achieve VIP scaling. The ADC VPX instance also provides high availability to the VIPs configured. After you configure VIP addresses as part of the metadata, you can configure an LB virtual server using the same IP that is used to create the forwarding rules. Thus, we can use forwarding rules to mitigate the limitations we have w.r.t scale in using public VIP addresses on an ADC VPX instance on GCP.
For more information on forwarding rules, seeForwarding rules overview.
For more information on HA, seeHigh Availability.
Points to note
- Google charges some additional cost for each virtual IP forwarding rule. The actual cost depends on the number of entries created. The associated cost can be found from the Google pricing documents.
- Forwarding rules are applicable only for public VIPs. You can use alias IP addresses when the deployment needs private IP addresses as VIPs.
- You can create forwarding rules only for the protocols, which need the LB virtual server. VIPs can be created, updated, or deleted on the fly. You can also add a new load balancing virtual server with the same VIP address but with a different protocol.
Before you start
- Citrix ADC VPX instance must be deployed on GCP.
External IP address must be reserved. For more information, seeReserving a static external IP address.
Ensure that your GCP service account has the following IAM permissions:
REQUIRED_IAM_PERMS = [ "compute.addresses.list", "compute.addresses.get", "compute.addresses.use", "compute.forwardingRules.create", "compute.forwardingRules.delete", "compute.forwardingRules.get", "compute.forwardingRules.list", "compute.instances.use", "compute.subnetworks.use", "compute.targetInstances.create" "compute.targetInstances.get" "compute.targetInstances.use", ]
进行gure external IP addresses for VIP scaling on Citrix ADC VPX instance
- In the Google Cloud Console, navigate to theVM Instancespage.
- Create a new VM instance or use an existing instance.
- Click the instance name. On theVM instance detailspage, clickEdit.
- Update theCustom metadataby entering the following:
- Key = vips
Value = Provide a value in the following JSON format:
{ “Name of external reserved IP”: [list of protocols], }
GCP supports the following protocols:
- AH
- ESP
- ICMP
- SCT
- TCP
- UDP
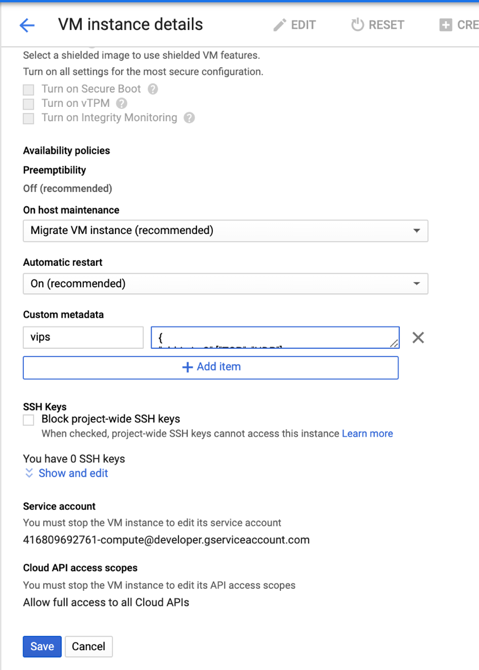
For more information, seeCustom metadata.
Example for Custom metadata:
{ “external-ip1-name”:[“TCP”, “UDP”], “external-ip2-name”:[“ICMP”, “AH”] }
In this example, the ADC VPX instance internally creates one forwarding rule for each IP, protocol pair. The metadata entries are mapped to the forwarding rules. This example helps you understand how many forwarding rules are created for a metadata entry.
Four forwarding rules are created as follows:
- external-ip1-name and TCP
- external-ip1-name and UDP
- external-ip2-name and ICMP
- external-ip2-name and AH
- ClickSave.
Setting up a load balancing virtual server with external IP address on a Citrix ADC VPX instance
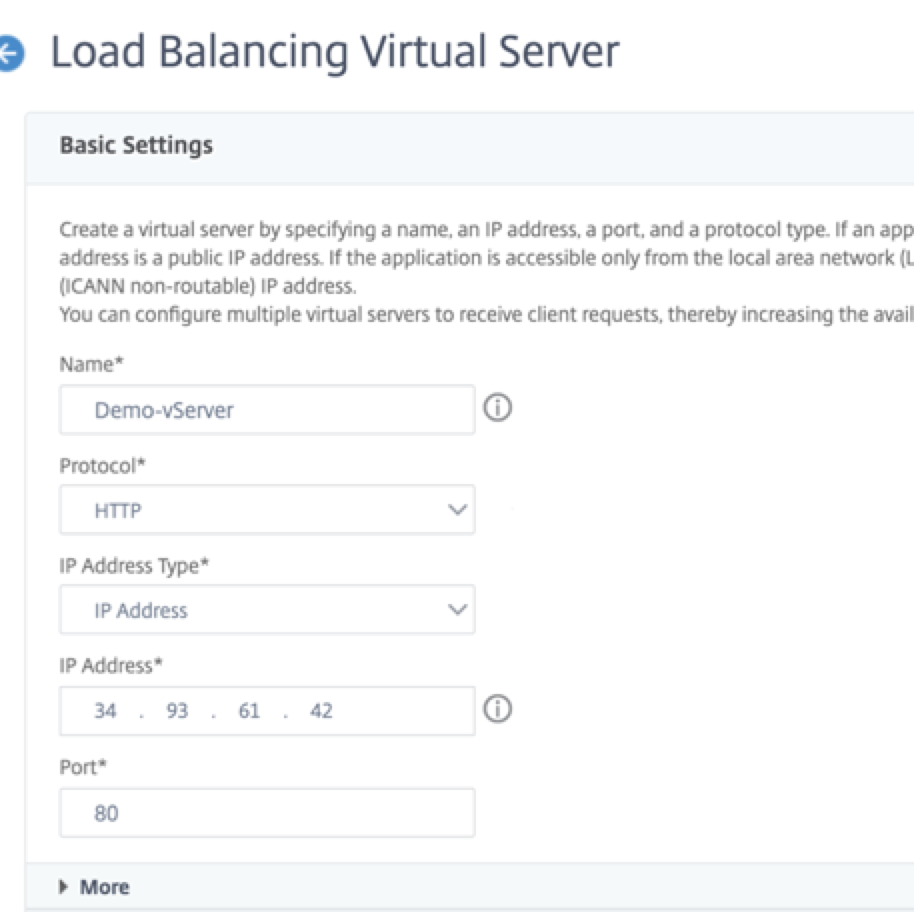
Step 1. Add a load balancing virtual server.
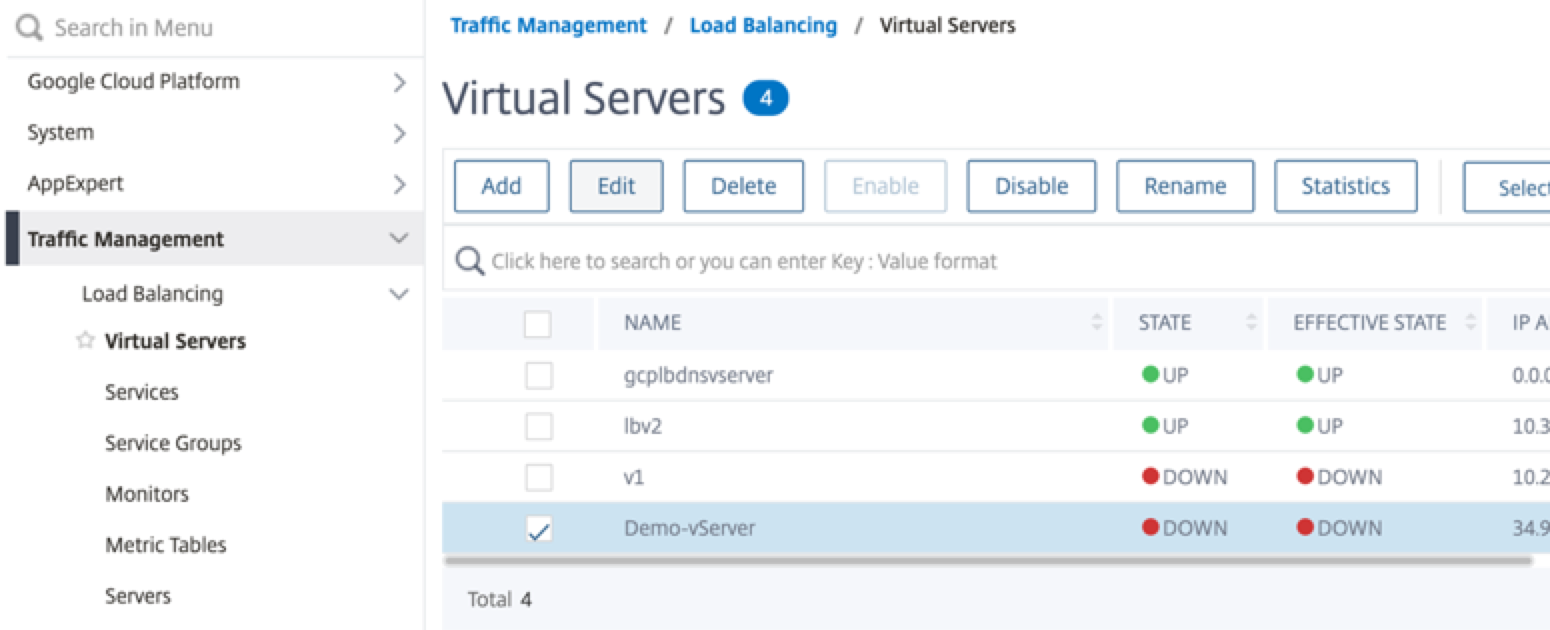
Navigate to进行guration > Traffic Management > Load Balancing > Virtual Servers > Add.
Add the required values for Name, Protocol, IP Address Type (IP Address), IP Address (External IP address of the forwarding rule that is added as VIP on ADC) and Port, and clickOK.
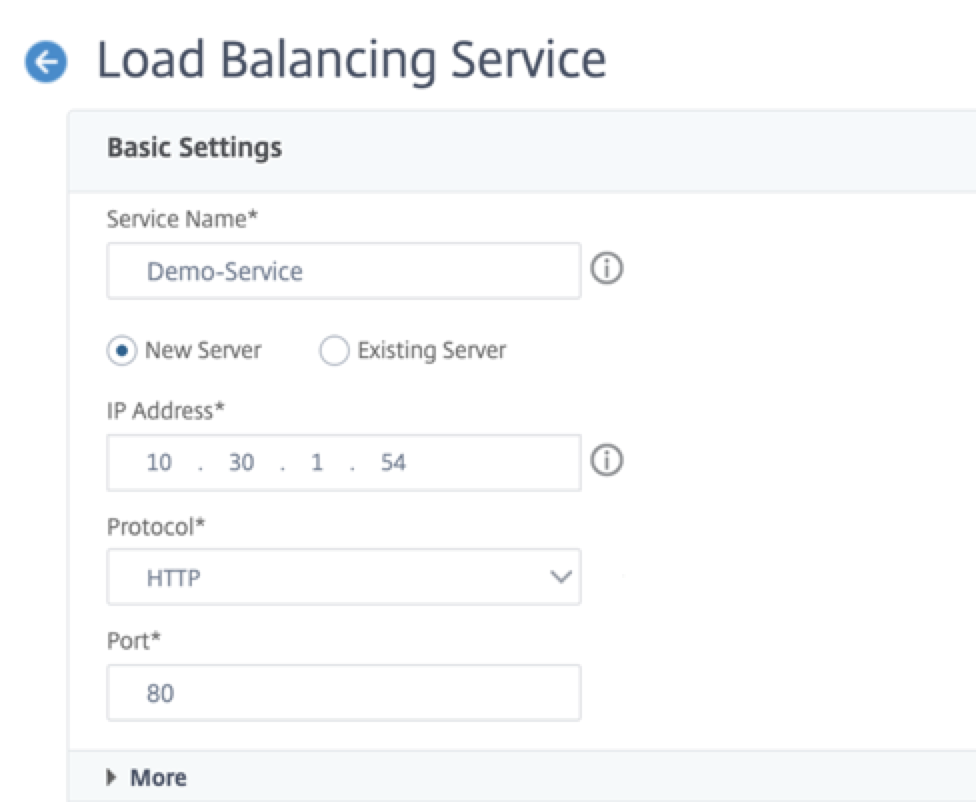
Step 2. Add a service or service group.
- Navigate to进行guration > Traffic Management > Load Balancing > Services > Add.
Add the required values for Service Name, IP Address, Protocol and Port, and clickOK.
Step 3. Bind the service or service group to the load balancing virtual server.
- Navigate to进行guration > Traffic Management > Load Balancing > Virtual Servers.
- Select the load balancing virtual server configured inStep 1, and clickEdit.
In theService and Service Groupspage, clickNo Load Balancing Virtual Server Service Binding.
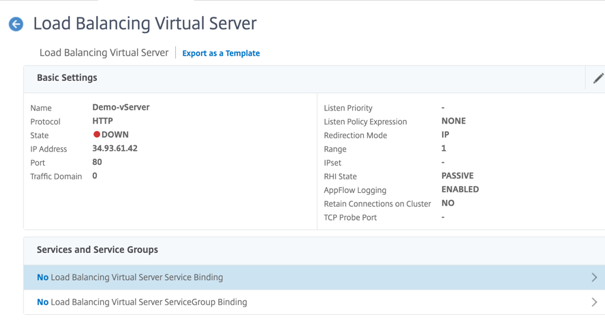
Select the service configured in theStep 3, and clickBind.
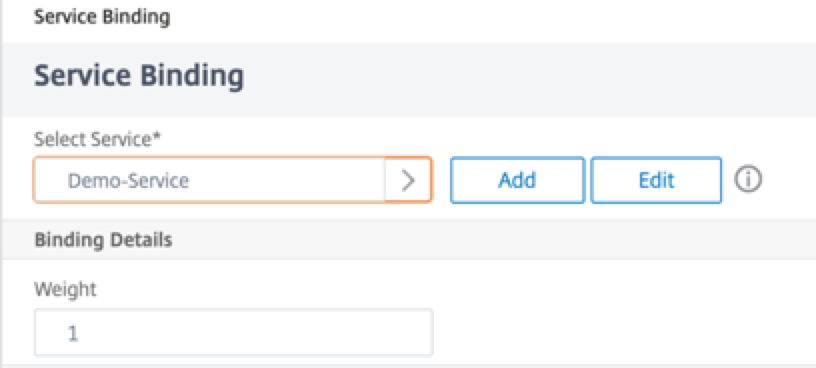
- Save the configuration.
Share
Share
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select Do Not Agree to exit.
